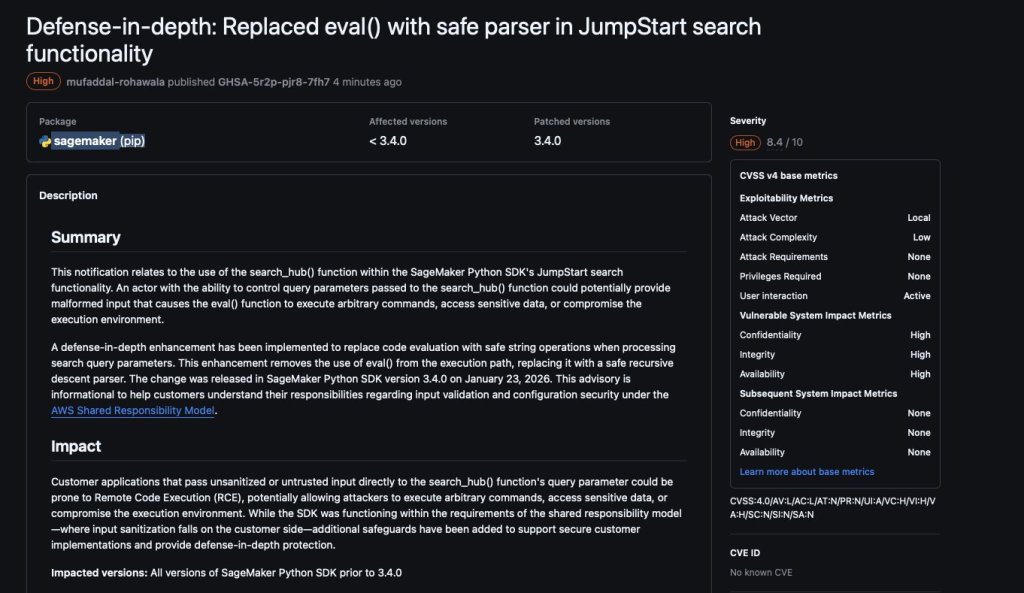
In January 2026 I reported a remote code execution risk in the Amazon SageMaker Python SDK affecting the JumpStart search functionality. The issue originated from the use of Python’s eval() to process user-controlled filter expressions.
Although the evaluation attempted to restrict execution by removing __builtins__, Python’s runtime object model allows traversal through class hierarchies that can escape such restrictions. This made the sandbox ineffective and enabled arbitrary code execution in the process running the SDK.
AWS investigated the report, implemented a remediation, and released the fix in sagemaker-python-sdk v3.4.0.
I would like to thank the AWS Security team for their professional coordination during the disclosure process.
Background
+++++++++++
Amazon SageMaker JumpStart provides a catalog search capability that allows developers to filter models using logical expressions.
The filtering logic was implemented in _Filter.match():
def match(self, keywords: List[str]) -> bool:
expr = self._convert_expression(self.expression)
return eval(expr, {“__builtins__”: {}}, {“keywords”: keywords, “any”: any})
The intention was to evaluate a limited expression grammar (logical filters and keyword matching) in a restricted environment.
The assumption was that removing __builtins__ would prevent arbitrary execution.
Unfortunately, this assumption is incorrect in Python.
Why the Sandbox Failed
++++++++++++++++++++
Python objects expose extensive introspection capabilities. Even when built-ins are removed, existing runtime objects can be used to reach powerful primitives.
A common technique begins with traversing the base object hierarchy:
().__class__.__bases__[0].__subclasses__()
This returns every subclass loaded in the interpreter. Among these are classes whose methods expose global namespaces or imported modules such as os or subprocess.
From there, arbitrary system commands can be executed.
Because JumpStart search evaluated filter expressions directly, a malicious query could trigger this traversal and achieve code execution.
Exploit Surface
+++++++++++++
The vulnerable function was reachable through JumpStart search:
search_hub(query)
In practice this function appears in many environments:
• SageMaker Studio notebooks
• developer scripts
• example tutorials
• CI pipelines or automation workflows
If a malicious filter string reaches the search function—directly or indirectly—it can execute code inside the developer environment running the SDK.
This vulnerability affected client-side search logic only and did not impact SageMaker infrastructure, model training, or hosted endpoints.
The Fix
+++++++
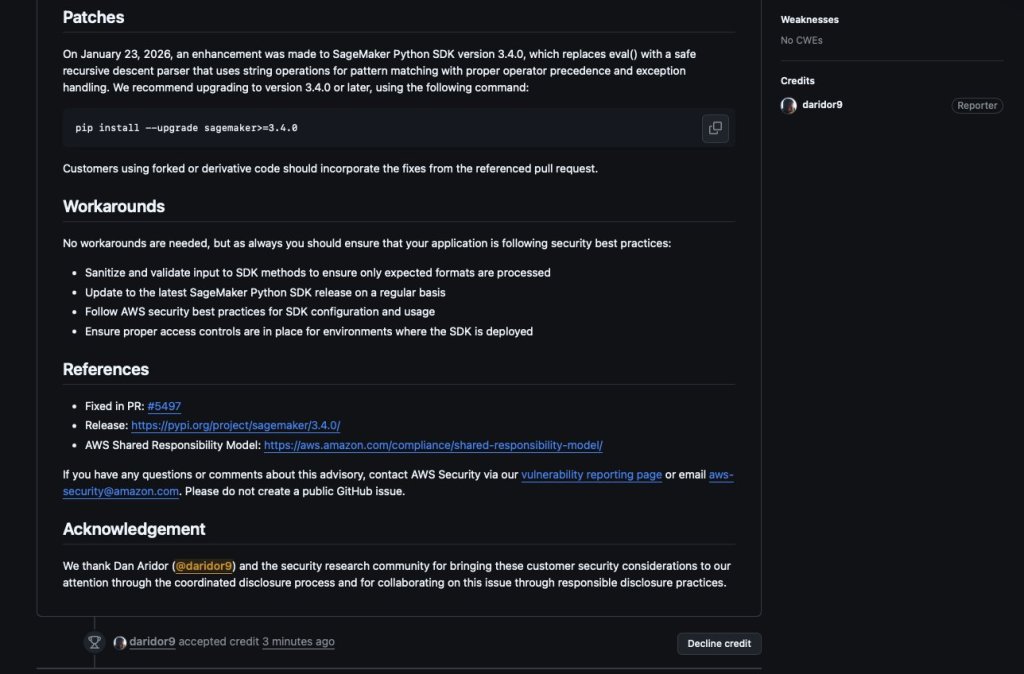
AWS removed the eval()-based evaluation and replaced it with a dedicated parser.
The new implementation introduces explicit node types representing the supported grammar:
* _AndNode
* _OrNode
* _NotNode
* _PatternNode
This preserves the intended filter semantics while eliminating the possibility of arbitrary code execution.
The remediation was released in sagemaker-python-sdk v3.4.0.
Timeline
+++++++
January 18, 2026 — Vulnerability reported to AWS
January 23, 2026 — AWS releases fix in v3.4.0
February 3–25, 2026 — Coordination on disclosure
March 2026 — Public disclosure
Recommendations
+++++++++++++++
Users of SageMaker JumpStart search functionality should upgrade to:
sagemaker-python-sdk ≥ v3.4.0
More broadly, developers should avoid evaluating user-controlled expressions using eval().
Even environments with empty built-ins are not safe against Python object graph traversal techniques.
For constrained expression grammars such as filters, the correct approach is to implement a dedicated parser or AST evaluator.
The “Fake Sandbox” Anti-Pattern
++++++++++++++++++++++++++
This vulnerability reflects a recurring security anti-pattern: attempting to sandbox eval().
In Python, the runtime environment already contains powerful objects and class hierarchies. Removing built-ins does not remove access to those objects.
As a result, many “restricted eval” designs fail under introspection-based escape techniques.
The safest architectural approach is to avoid code execution entirely when evaluating structured expressions.
Acknowledgment
++++++++++++++++
Thanks to the AWS Security Outreach team for the prompt response and collaborative handling of the disclosure.
AWS Official Statement
+++++++++++++++++++
“AWS is aware of a report describing a potential code execution scenario in the SageMaker Python SDK’s JumpStart search functionality, where user input was processed using eval() with an inadequate sandbox.
On January 23, 2026, AWS released SageMaker Python SDK version 3.4.0 that replaced the use of eval() with a safe recursive descent parser as a defense-in-depth feature enhancement. This change eliminates potential code execution paths in filter expression evaluation while maintaining full backward compatibility. Customers using SageMaker Python SDK versions prior to 3.4.0 should upgrade to version 3.4.0 or later. This can be updated via pip using the following command:
pip install –upgrade sagemaker>=3.4.0
This enhancement was implemented as part of AWS’s ongoing commitment to defense-in-depth and customer security. The updated implementation employs safe string operations with proper operator precedence and robust exception handling, delivering equivalent functionality without relying on code evaluation. Under the AWS shared responsibility model, we encourage customers to adopt the latest SDK version to benefit from this and other security improvements. Staying current with SDK updates is one of the most effective steps customers can take to maintain a strong security posture in their environments.
We appreciate the security research community for reporting this concern and collaborating with AWS.
[1] https://pypi.org/project/sagemaker/3.4.0/
[2] https://github.com/aws/sagemaker-python-sdk/pull/5497“
++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++
“We thank Dan Aridor (@daridor9) and the security research community for bringing these customer security considerations to our attention through the coordinated disclosure process and for collaborating on this issue through responsible disclosure practices.”